The GERD Trilateral Talks: what is next?
The GERD Trilateral Talks: what is next?
Bethlehem Mehari

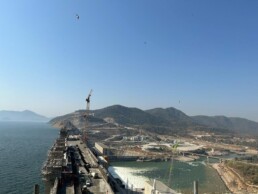
The Nile, the longest river in the world, passes through eleven countries; distinctly shaping each of their economies, political, and social lives. The Blue Nile, known to the Ethiopians as Abbay, one of the major tributaries of the Nile has been at the center of international attention following Ethiopia`s commencement of the construction of a mega dam known as the Grand Ethiopian Renaissance Dam (GERD) in 2010. The GRED is intended to harness the country’s immense hydroelectric potential to bring electricity to more than half of its destitute population living without access to electricity and all associated services and infrastructure. Since the inauguration of the project, Ethiopia, the dam owner along with the two lower riparian countries Egypt and Sudan, has been in a negotiation marathon without an end in sight. As the Dam is under construction on a transboundary river, negotiating with the two lower riparian states on how to fill it and operate it was needed.
Egypt perceives the project as a “security threat” in that it challenges its self-claimed “historical right” over the Nile waters. Though the basis for this “historical right” is flawed and unrecognized by Ethiopia and the rest of the upstream riparian states of the Nile, it is evident that GERD challenges the existing status quo in the use of the Nile Waters.
Sudan’s position, on the other hand, seems ever-evolving with its changing leadership.
Sudan’s position, on the other hand, seems ever-evolving with its changing leadership. Whilst initially favorable to the economic and cooperative prospects the dam brings, Sudan has, as of late following the revolution in the country in 2019, aligned with the Egyptian position. Understanding their approach was against their self-interest, Sudan returned to its initial approach: cooperating with Ethiopia.
The signing of the Declaration of Principles on the Grand Ethiopian Dam Project (GERDP) in March 2015 was seen as a significant milestone toward reaching a shared understanding not only on the dam but also on the Nile. The agreement outlines the core principles that should govern the three riparian states. The 2015 DoP agreement, which stipulates that “The three Countries shall utilize their shared resources in their respective territories in an equitable and reasonable manner” (Article 4) stands in stark contrast with Egypt’s assertions of “historical right.” This historical right, with colonial roots in the early 20th century, entitles Egypt to 55.5 BCM of the Nile waters, 18.5 BCM for Sudan, and leaving the remaining more than 10 BCM of water for evaporation. This entitlement is further entrenched in Article 44 of the Egyptian constitution which, not only disregards the natural rights and interests of all upstream states it inexorably securitizes an otherwise cooperative shared resource.
“The “historical right” argument, often evoked by Egyptian politicians, effectively leaves no room for a “dialogue of equals.” Rather, it establishes Egypt as the sole and proprietary authority over the Nile and all future projects on the Nile.
The “historical right” argument, often evoked by Egyptian politicians, effectively leaves no room for a “dialogue of equals.” Rather, it establishes Egypt as the sole and proprietary authority over the Nile and all future projects on the Nile. This applies not only to Ethiopia’s GERD project but also to all other riparian states, setting a dangerous monopolistic precedent over the Nile. Despite the promising provisions on “equitable and reasonable use” forwarded by the agreement, the parties are yet to agree on the guidelines and rules on the GERD, i.e. a non-consumptive project. So, what are the sticking points that have stalled an agreement by over a decade?
Current talks:
The GERD negotiations have passed through several iterations under several facilitators. The latest talks (September, 23) which took place in Addis Ababa, were initiated by Prime Minister Abiy Ahmed during his Cairo visit on the 12th and 13th of July. The Egyptian and Ethiopian leaders jointly set an ambitious plan to produce the “Guidelines and Rules on the Annual Filling and Operation of the Dam” within four months.
The first meeting of the current process, which took place in Cairo in late August, concluded without progress.
According to sources close to the negotiations, members of the Sudanese delegation expressed their frustrations that the Cairo process created a divergence rather than a convergence of interests, which would have inched the parties closer to an agreement.
According to the same source, the recent divergence of positions was due to the Egyptian delegation’s introduction of “new texts and concepts” which are not only foreign to the current process but contrary to the 2015 trilateral Declaration of Principles Agreement.
The Egyptian delegation is reported to have forwarded new terms and concepts that would be seen as outside of the scope of the framework established in 2015.
Sources who attended the Addis-Ababa talks cite the same problem for yet another inconclusive meeting. The Egyptian delegation is reported to have forwarded new terms and concepts that would be seen as outside of the scope of the framework established in 2015. Given that the aforementioned DoP agreement is the only international legal document governing the relationship of the three countries as it relates to the Dam, it is highly unlikely that the three nations can ever reach an agreement, let alone within the 4-month timeframe the leaders have ambitiously set forth.
Is there a shared understanding of the basics?
As the talks currently stand, no. Sources say that the Ethiopian and Sudanese delegations continue to uphold the 2015 Declaration of Principles agreement as a live document that should encapsulate subsequent GERD negotiations. The challenges in the current round of negotiation arise distinctly from Egypt’s refusal to stay within the scope of the 2015 agreement. The Egyptian delegation, by insisting on new terms and conditions, seems intent on stepping outside the framework of the 2015 agreement, further stalling the prospects for a possible agreement.
The 2015 Declaration of Principles document, as it is the only agreement signed between the three riparian states, should serve as a guiding document; at the very least, the parties must endeavor to uphold the principles therein. However, should Egypt continue to undercut its the 2015 agreement, is there another such document that can serve as a basis for another agreement? Sources have disclosed that the 2015 DoP document was not made public- to the amazement of both Sudanese and Ethiopian delegations- Egypt’s delegates insisted on making the document public. It is now the same document that Egypt is almost opposing.
The Second position, as an extension of the first, is that the GERD reservoir must serve as Egypt’s secondary reservoir should drought affect the region.
Though the Sudanese presence was noticeably understated during the current rounds, as it stands, there are two primary indicators of the Egyptian position during both the Cairo and Addis Ababa talks. The first is a complete rejection of Ethiopia’s equal “ownership” of the Nile and inalienable rights to use its natural resources. The Second position, as an extension of the first, is that the GERD reservoir must serve as Egypt’s secondary reservoir should drought affect the region. The Ethiopian delegation stands starkly opposed to these positions reflected by the Egyptian delegation as it reportedly steered the discussion toward an Egyptian monopoly.
In the case of drought, the Ethiopian position is that a region-wide drought-mitigation mechanism should be put in place. According to international law and customs, there is no other nation with a transboundary river that has committed to singularly availing its water reserves for another riparian state. The Ethiopian delegation, as it has during past talks, insists that regional-level solutions must be formulated for regional-level disasters such as drought.
What is next?
As a process initiated and overseen by the negotiating parties themselves, this current progress encouraged optimism. However, in addition to past issues of contention like information sharing, drought mitigation, and filling timeline- this process is further scattered in focus due to the shift away from the 2015 DoP. This pursuit of arriving at a shared understanding is made evermore elusive due to megaphone diplomacy, oft deployed by Egypt, for political expediency. The progress, or lack thereof, made in the Addis Ababa talks also casts doubt on the prospects for a progressive outcome in the upcoming October 23-24 talks to be held in Cairo.
Bethlehem is the Director and Editor-in-Chief at Horn Review. As co-founder, she oversees research and training programs, as well as the editorial process at Horn Review.
Share
GERD: Striving for Survival and Fighting False Narratives
GERD: Striving for Survival and Fighting False Narratives
By Silabat Manaye

Silabat Manaye is international relations professional based in Addis Ababa. His research interests include water politics, geopolitics in the Horn of Africa, and War Journalism. He authored two books on Nile geopolitics.
Hydro-diplomacy plays a crucial role in fostering cooperation and negotiation among countries sharing water resources. The recent completion of the 4th filling of the Grand Ethiopian Renaissance Dam (GERD) by Ethiopia without significant impacts on downstream countries, Sudan and Egypt, indicates positive developments in hydro-diplomacy efforts. This article analyzes key points derived from the recent statements of the Ethiopian Government on the completion of the 4th filling of the Grand Ethiopian Renaissance Dam (GERD) and the potential for increased cooperation in managing water resources in the Nile basin.
No Significant Impact on Water Volume
With the first four fillings of the GERD showing no effect on the Nile River’s flow towards Sudan and Egypt, Ethiopia’s cautious management of the dam’s operations becomes evident. This cautious approach indicates Ethiopia’s commitment to mitigating potential negative impacts on downstream countries and promoting a constructive hydro-diplomatic approach. By safeguarding the interests of neighboring countries, Ethiopia exhibits a willingness to cooperate and maintain the ecological balance and livelihoods of communities in Sudan and Egypt.
Reassurance of Good Intentions
The completion of the first four fillings serves as evidence of Ethiopia’s intentions to avoid causing significant harm to downstream countries. This accomplishment is crucial for building trust and fostering cooperation among riparian countries. By assuring Sudan and Egypt that the GERD operations will not cause significant harm to their livelihoods, Ethiopia aims to establish a foundation of trust and collaboration. This reassurance is a pivotal component of successful hydro diplomacy, highlighting Ethiopia’s commitment to addressing concerns and promoting cooperation.
Unwarranted Claims over the GERD
The completion of the first four fillings challenges Egypt’s exaggerated fears of a water shortage by emphasizing Ethiopia’s successful completion of the fourth filling. By demonstrating that these exaggerated concerns are unwarranted, Ethiopia aims to invalidate Egypt’s claims and reduce international support for these fears. Through dispelling misconceptions surrounding the GERD, Ethiopia strives to foster a more constructive and cooperative dialogue with Egypt and other riparian countries. Addressing misinterpretations is critical for advancing hydro diplomacy efforts and promoting understanding among all stakeholders.
GERD and Population Growth
The construction of the Grand Ethiopian Renaissance Dam (GERD) in the Nile Basin has been a subject of intense debate and controversy. However, understanding the rationale behind the decision to build this massive hydropower dam requires a closer examination of the social and economic shifts within Ethiopia. In the past century, Egypt held a position of social and economic dominance within the Nile Basin, fueled by its rapid population growth. However, this balance began to change over time as Ethiopia witnessed a surge in population growth. According to recent data from the Worldometer (2022), the population of Ethiopia surpassed that of Egypt.
Ethiopia currently has a booming economically engaged population in need of energy, jobs, and economic possibilities as its population grows. Access to energy capacity has become a critical issue in Ethiopia’s ability to sustain growth and development. Despite Ethiopia’s expanding goals, the country’s inability to obtain adequate energy capacity has limited its economic potential.
As a result, Ethiopia’s government looked to a massive hydroelectric dam as a way to fulfill its energy needs while also fostering economic growth.
Survival also became a driving force behind the construction of the GERD. With a rapidly expanding population and limited resources, Ethiopia faced pressing questions regarding its long-term sustainability. Developing the GERD became a strategic response to secure a sustainable future for Ethiopia, ensuring access to water, energy, and economic opportunities.
Egypt’s Long-standing Hegemony over Nile
Egypt’s “water security” strategy is built on a fixation with the Nile River, with the goal of obstructing all avenues that could lead to an equitable distribution of the Nile’s waters. When any basin country lays out a strategy to utilize Nile water on its own territory, the Egyptians frequently respond with war threats and conflict-laden remarks. When requested to renegotiate the distribution of water in the basin, they set conditions by stating that colonial and postcolonial treaties are non-negotiable and that we can discuss anything else.
We believe that other riparian countries, like Egypt, have genuine ambitions to utilize the Nile’s waters. Ethiopia has already done so by launching and building the Grand Ethiopian Renaissance Dam (GERD). The contemporary geopolitical realities in the Nile Basin do not allow for the continuation of colonial-period agreements. Egypt’s hegemony over the Nile River Basin has been stuck in time.
GERD and Hydro-diplomacy
Ethiopia’s completion of the 4th filling of the GERD presents an opportunity to revitalize hydro-diplomacy in the region. By demonstrating its cautious approach and commitment to cooperation, Ethiopia is sending a clear message to Sudan, Egypt, and other riparian countries that it values their concerns and seeks a mutually beneficial solution. Rather than viewing the GERD as a threat, stakeholders should see it as an opportunity for collaboration in managing the Nile’s resources for the greater benefit of all.
Negotiations and collaboration should be based on principles of equity, fairness, and respect for the sovereignty of all riparian countries. A fresh start is needed to address historical grievances and move towards a more inclusive and sustainable water management system. The completion of the fourth filling should serve as a catalyst for renewed dialogue and trust-building among all involved parties.
The completion of the fourth filling of the GERD marks a significant achievement for Ethiopia. It showcases the country’s ability to construct and manage a mega dam while minimizing harm to downstream countries. Ethiopia’s cautious approach and commitment to addressing concerns demonstrate its willingness to promote hydro diplomacy and collaboration among riparian countries. By dispelling misconceptions and challenging colonial-era agreements, Ethiopia aims to foster a more inclusive and equitable water management system for the Nile River. The fourth filling presents an opportunity for all stakeholders to revitalize hydro diplomacy and work together towards a sustainable and mutually beneficial solution. The rationale behind the development of the GERD cannot be understood in isolation but must be viewed through the lens of social and economic shifts in the Nile Basin. As upstream states experience rapid population growth and the emergence of a new economically active population, the need for energy capacity becomes critical. The GERD is a deliberate step to address these needs, assure long-term growth and development for the basin’s states, and address Ethiopia’s survival issue.
Share
China's Expanding Arms Dealing in Africa: Yet another threat to the Peace and Security of the Continent
China's Expanding Arms Dealing in Africa: Yet another threat to the Peace and security of the Continent
By Staff Writer
China’s increasing involvement in arms dealing in Africa has raised concerns about the potential implications for the continent’s peace and security. As China expands its economic and political influence in Africa, its arms sales to various African nations have also witnessed a rapid surge, and this trend demands a closer analysis of its impact on the peace and security in the region.
China’s strategic decision to expand its arms trade with African nations has been primarily driven by economic and geopolitical objectives. African countries often find Chinese arms deals attractive due to lower costs compared to Western alternatives and a more lenient approach to human rights concerns. However, it is important to recognize that this expansion comes at a cost that undermines the continent’s peace and security.
China’s arms sales to African nations pose a direct threat to the peace and security of the continent. The proliferation of weapons perpetuates conflict and exacerbates existing tensions between states. Additionally, the influx of cheap Chinese weapons often ends up in the hands of non-state armed groups, further destabilizing regions and fueling civil wars and insurgencies.
Furthermore, China’s arms dealing expansion in Africa not only contributes to conflicts but also obstructs efforts made by international organizations to mediate and resolve these conflicts. African Union peacekeeping missions, supported by international partners, have been working tirelessly to pacify war-torn regions. However, the availability of Chinese weapons often bolsters the capabilities of belligerent parties, thereby prolonging conflicts and jeopardizing peacekeeping efforts.
Moreover, China’s arms trade in Africa and its potential impact on peace and security extend beyond the direct provision of weapons. The rapid expansion of Chinese arms sales in the continent inadvertently enables the emergence of proxy wars, wherein rival factions supported by different external actors engage in conflict on African soil.
This intensification of proxy wars not only endangers the lives of countless Africans but also exacerbates regional tensions, potentially leading to a wider regional instability.
China’s assertive expansion of arms dealing in Africa is not without self-interest. Aside from economic gains, China also seeks access to strategic resources and political influence across the continent. By providing weapons and military equipment, China cultivates political alliances with African countries, often undermining good governance and human rights considerations. This reinforces the notion that China’s arms deals in Africa serve not only as a means to secure economic interests but also as a tool to enhance its geopolitical influence on the continent.
China’s thriving arms dealing expansion in Africa holds significant implications for the peace and security of the continent. The proliferation of cheap Chinese weapons exacerbates conflicts, empowers non-state actors, hampers peacekeeping operations, and fuels proxy wars. Moreover, this unregulated expansion by China undermines efforts to achieve lasting peace and stability in Africa.
To address this issue, African nations need to engage in stronger regional cooperation, bolster arms control frameworks, and actively seek alternative sources of security cooperation beyond Chinese arms deals. Additionally, the international community, including regional organizations and major powers, must hold China accountable for its actions and work towards establishing a more comprehensive and regulated arms trade regime that prioritizes promoting peace and security over individual state interests.
By acknowledging the detrimental impact of China’s arms dealing expansion in Africa and taking proactive steps, Africa can ensure a secure and stable future for its people, free from external interventions that intensify conflicts and hinder socio-economic development.
Share
The Wheat Politics and War - How should Africa navigate?
The Wheat Politics and War - How should Africa navigate?
By Staff Writer

The wheat politics of Russia and Ukraine have had a significant impact on Africa, both positive and negative. These two countries are major exporters of wheat, and their policies, production levels, and export dynamics have influenced food security, domestic markets, and agricultural development in various African nations. However, this influence has not always yielded beneficial outcomes, and addressing these challenges requires exploring alternative strategies and potential solutions.
Russia and Ukraine are known as the breadbaskets of Europe, producing vast quantities of wheat every year. Their agricultural policies and export competitiveness significantly affect global wheat prices, including those in Africa. In recent years, increased competition and improved efficiency in the wheat sector of these countries have resulted in expanded production and lowered prices, benefiting African consumers by making wheat more accessible and affordable. Reduced prices have played a vital role in enhancing food security in Africa, where wheat is a staple food and a primary source of nutrition.
However, the impact of Russia and Ukraine’s wheat politics on Africa is not solely positive. The fluctuation of wheat prices on the global market has created both opportunities and challenges for African wheat producers. When international wheat prices are low, domestic wheat farmers in Africa struggle to compete and may face difficulties in selling their produce. As a result, this discourages domestic cultivation and negatively affects the long-term growth and self-sufficiency of African agricultural sectors. Therefore, while African consumers benefit from lower prices, the livelihoods of local farmers are at stake.
Furthermore, dependence on wheat imports from Russia and Ukraine poses a risk to African food security. Due to the dominance of these countries in the global wheat market, any disruption in their export capacity, whether caused by geopolitical tensions, trade restrictions, or climate related challenges, could have severe consequences for African countries heavily reliant on imported wheat.
This vulnerability was clearly demonstrated in 2010 when a severe drought in Russia led to a substantial decrease in its wheat production and subsequent export restrictions. As a result, African nations faced skyrocketing wheat prices and scarcity, exacerbating food insecurity in the region.
Addressing the challenges posed by the wheat politics of Russia and Ukraine requires exploring alternative strategies and potential solutions. African nations can invest in improving domestic wheat production capabilities through technological advancements, enhanced farming practices, and infrastructural development. By increasing productivity and reducing dependence on imports, African countries can mitigate the risks associated with global price fluctuations and export disruptions.
Furthermore, regional cooperation among African nations can play a crucial role in mitigating food security risks. By fostering intra-African trade in wheat and other agricultural commodities, countries can diversify their import sources, reducing reliance on any single country or region. Moreover, collective action can strengthen the bargaining power of African nations in global markets, enabling them to negotiate better terms of trade.
Lastly, increased investment in research and development is crucial for boosting agricultural productivity in Africa. This involves developing drought-resistant wheat varieties better suited to the continent’s climate and investing in irrigation infrastructure to mitigate the risks posed by irregular rainfall patterns. By embracing innovative agricultural technologies and sustainable practices, African countries can enhance their agricultural capacities and reduce dependence on imported wheat.
It is certain that the wheat politics of Russia and Ukraine have a profound impact on Africa and while lower global wheat prices benefit African consumers, they pose challenges for domestic farmers and food security. Addressing these challenges requires investment in domestic wheat production, regional cooperation, and research and development. By enhancing African agricultural capabilities and reducing dependency on imported wheat, African nations can mitigate the risks associated with global price fluctuations and export disruptions, ultimately improving food security and fostering sustainable agricultural development.
Share
President Afewerki's Diplomatic Moves and Eritrea's Backing of China and Russia
President Afewerki's Diplomatic Moves and Eritrea's Backing of China and Russia
By Staff Writer

In recent years, Eritrea, a small East African nation known for its long-standing isolation, has undergone a significant shift in its diplomatic relations. President Isaias Afewerki has been instrumental in steering Eritrea towards closer partnerships with global powers like China and Russia. This essay aims to explore the recent diplomatic overtures made by President Afewerki and weigh Eritrea’s motivations for leaping closer to these two global powers.
Diplomatic Shift:
The President Afewerki’s diplomatic moves signify a departure from Eritrea’s previously isolated stance on the world stage. Historically, Eritrea’s relations with the international community were strained due to its involvement in regional conflicts and its skepticism of foreign intervention. However, in recent years, President Afewerki has actively sought to cultivate new diplomatic ties, particularly with China and Russia.
Backlash and the Ends Justifying the Means:
This diplomatic shift has faced criticism from various international actors who question the motives and consequences of Eritrea’s alignment with China and Russia. Critics argue that Eritrea’s newfound alliances are merely an attempt to gain more support against Western influence, rather than advancing the nation’s socioeconomic development. However, one must consider Eritrea’s unique historical context and the complex regional dynamics it faces before making a determination on the potential benefits and drawbacks.
Motivations behind the Partnerships:
Eritrea’s backing of China and Russia can be attributed to several underlying factors. Firstly, China and Russia’s increasing global influence and economic power makes them attractive partners for a nation seeking economic growth and infrastructure development. China has become Africa’s largest trading partner, and Russian investments in the continent have also been on the rise.
By aligning with these countries, Eritrea hopes to tap into their resources to stimulate its own development.
Additionally, Eritrea’s diplomatic moves can be understood within a regional context. The country faces several challenges, including regional conflicts, refugee crises, and terrorism threats. By aligning itself with China and Russia, Eritrea aims to enhance its security and ensure stability in the region. With China’s growing presence in Africa and Russia’s increased involvement in Middle Eastern affairs, Eritrea sees an opportunity to strengthen its security capabilities through these alliances.
Implications for Eritrea’s Future:
Eritrea’s partnerships with China and Russia have the potential to bring about positive and negative consequences. On the one hand, increased investment from China could boost Eritrea’s infrastructure and spur economic growth. This could lead to job creation, poverty reduction, and improved living standards for the Eritrean people. Similarly, Russia’s involvement may help address regional security concerns, leading to stability and the possibility of increased regional cooperation.
There are, however, potential drawbacks as well. Eritrea’s reliance on China and Russia could result in overdependence, jeopardizing its sovereignty and autonomy. Moreover, concerns have been raised about human rights abuses and environmental degradation associated with some Chinese investments in Africa, and Eritrea needs to carefully navigate these issues to protect its long-term interests.
President Isaias Afewerki’s diplomatic moves to align Eritrea with China and Russia mark a significant shift in the country’s foreign policy. These partnerships are motivated by a desire for economic growth, infrastructure development, and regional security. While the alliances offer unique opportunities for Eritrea, careful consideration must be given to ensure Eritrea’s long-term interests are protected and that the nation avoids overdependence on these global powers. By strategically managing these relationships, Eritrea can potentially leverage the resources and expertise of China and Russia to overcome its development challenges and foster a more prosperous and stable future.
Share
Wagner (PMC) and its Operations in Africa
Wagner (PMC) and its Operations in Africa
By Staff Writer

The killing of Yevgeny Prigozhin, a Russian oligarch and the alleged owner of the private military company Wagner, has sent shockwaves throughout the international community. The incident, which occurred in Africa, has raised concerns about the expansion of Wagner’s influence in the continent and its potential implications for global security. As the dust settles, it is crucial to assess the future of Wagner in Africa and consider the consequences it may have.
Wagner, a paramilitary organization composed of Russian mercenaries, has gained notoriety for its involvement in conflicts in Ukraine and Syria. Its operations are believed to be supported by the Russian government, which denies any direct links but acknowledges that Russian citizens may join the group voluntarily. The killing of Prigozhin, who was reportedly known as “Putin’s chef” due to his close ties to the Russian president, raises questions about the extent to which the Russian government may be involved in Wagner’s activities.
Africa has become an area of interest for Wagner’s expansionist ambitions in recent years. The company has reportedly conducted military operations in Sudan, Libya, and the Central African Republic (CAR). In Sudan, many have alleged that Wagner played a significant role in supporting the former regime of President Omar al-Bashir, further exacerbating the ongoing political crisis in the country. In Libya and the CAR, Wagner’s presence has fueled conflict, hampering the prospects for peace and stability in these fragile nations.
The killing of Prigozhin adds a new layer of complexity to the situation. While the motive behind his assassination remains unclear, some speculate that it could be a result of internal power struggles within the ranks of Wagner and Wagner’s recent failed mutiny. If this is the case, it raises concerns about the stability and accountability of the organization.
The absence of clear leadership could lead to increased volatility and unpredictability in Wagner’s actions.
Moreover, the killing of Prigozhin has broader implications for the future trajectory of Wagner in Africa. It is unclear how his death will impact the group’s operations and the level of support it receives from the Russian government. If the Russian state perceives Wagner as a liability following this incident, it may choose to distance itself from the group, making it harder for Wagner to sustain its activities in Africa. On the other hand, if the Russian government perceives Wagner’s actions as aligned with its interests, it may continue to support and enable the group’s expansion in the continent.
The presence of Wagner in Africa has raised concerns about the potential consequences for regional stability and global security. The group’s activities have been characterized by a lack of accountability, disregard for human rights, and a tendency to exacerbate existing conflicts. These dynamics could lead to further destabilization, hindering efforts for peacebuilding and development in Africa.
To mitigate these risks, it is imperative for the international community to closely monitor and address Wagner’s presence in the continent. Diplomatic efforts should be aimed at discouraging African governments from engaging the services of private military companies like Wagner, focusing instead on strengthening their security forces and institutions. Additionally, international actors should continue to advocate for transparency, accountability, and respect for human rights in conflict-affected regions where Wagner operates.
In conclusion, the killing of Prigozhin and the future of Wagner in Africa require scrutiny and proactive engagement from the international community. The incident highlights the potential challenges posed by private military companies and their activities in fragile regions. It also underscores the need for increased cooperation and coordination among states to prevent the proliferation of such groups and reduce the negative impact on global security. With thoughtful and robust action, it is possible to address the concerns raised by Wagner’s presence in Africa, ensuring a more peaceful and stable future for the continent.
Share
Ethiopia's Entry into BRICS: Assessing Benefits and Risks for Domestic Development and Western Relations
Ethiopia's Entry into BRICS: Assessing Benefits and Risks for Domestic Development and Western Relations
By Staff Writer

Ethiopia, a rapidly developing African nation, has caught the attention of global economic powers due to its promising growth potential and strategic location. Amidst this context, the possibility of Ethiopia joining the BRICS group – comprising Brazil, Russia, India, China, and South Africa – raises important questions about the potential benefits and risks for the country’s domestic development and its relationship with Western powers. This brief article will delve into the key advantages, risks, and potential implications of such a move for Ethiopia.
Potential Benefits for Ethiopia
1. Enhanced Economic Cooperation: Joining BRICS would allow Ethiopia to deepen its economic cooperation with emerging markets. By tapping into the immense potential of BRICS countries, Ethiopia can benefit from increased trade opportunities, foreign direct investment, and access to technology. This partnership would amplify Ethiopia’s economic growth, diversify its export markets, and provide broader opportunities for its emerging industries, particularly in agriculture, manufacturing, and the service sector.
2. Infrastructure Development: Being a member of BRICS could provide Ethiopia with access to funding and expertise for much-needed infrastructure development projects. BRICS nations have a history of investing heavily in infrastructure, and Ethiopia could benefit from such knowledge transfer and financial support. Improved infrastructure, including transportation and energy networks, would attract more investments and stimulate industrial growth, facilitating Ethiopia’s progression towards becoming a middle-income country.
3. Strengthened Political and Regional Influence: For Ethiopia, BRICS membership would bolster its political influence on the international stage. By aligning itself with emerging powers who advocate for multipolarity in global affairs, Ethiopia can enhance its role in shaping regional policies and fuel the collective representation of emerging economies. This increased influence within BRICS forums would provide Ethiopia with a platform to raise its concerns, advocate for Africa’s interests, and accelerate the realization of the African Union’s development goals.
Risks and Challenges
1. Dependency and Partnership Imbalance: Ethiopia must be vigilant to avoid becoming overly dependent on
certain BRICS countries, particularly China, in economic and political spheres. To mitigate this potential risk, Ethiopia should aim for balanced partnerships that diversify its relationships with BRICS members and engage in responsible debt management strategies.
2. Western Powers’ Reaction: Ethiopia’s entry into BRICS could create friction with Western powers that might perceive this move as a diminishing influence on the African continent. Consequently, Ethiopia must take proactive steps to assure Western nations that its BRICS membership is not intended to replace existing partnerships but to complement them, ultimately fostering mutually beneficial cooperation in a multipolar global system.
3. Possible Clash of Values: Ethiopia’s alignment with BRICS could potentially challenge its domestic and Western-backed democratic and human rights standards. Confronting this concern, Ethiopia must ensure that its entry into the BRICS group does not compromise its commitment to democratic governance and adherence to universally recognized human rights norms.
Potential Implications for Relations with Western Powers:
Ethiopia’s membership in BRICS could potentially strain its relationship with Western powers, particularly those that provide substantial aid and investment. However, it is crucial to emphasize that Ethiopia’s engagement with BRICS does not have to be a zero-sum game at the expense of Western partnerships. Through skillful diplomacy and transparent communication, Ethiopia can assure Western powers that its BRICS membership serves to complement existing relationships, not undercut them. This would help maintain cordial ties, trade links, and continued cooperation on development projects and socio-political reforms initiated by Western partners.
Ethiopia’s potential entry into the BRICS group presents an opportunity for the nation to shape its future in various spheres, including economic growth, infrastructure development, and political influence. Despite potential risks and challenges, Ethiopia’s assertive membership in BRICS can positively impact its domestic development, provided it maintains a balanced approach, avoids over-dependency on specific BRICS nations, and continues to uphold democratic values and human rights. While navigating its relationship with Western powers, Ethiopia should convey its commitment to mutually beneficial cooperation and ensure that its BRICS membership complements, rather than undermines, existing partnerships.
Share
Africa's Debt to China and Concerns Surrounding its Impact on Local Businesses
Africa's Debt to China and Concerns Surrounding its Impact on Local Businesses
By Staff Writer
As Africa grapples with the pressing need for economic growth and infrastructure development, its increasing debt to China has become a cause for concern. While the Chinese government’s investments and loans have undoubtedly opened the doors to crucial developments, an alarming trend has emerged, signaling potentially detrimental consequences for local businesses across the continent. This article aims to shed light on Africa’s mounting debt to China and delve into the underlying issues that are stifling local entrepreneurship and economic self-reliance, thereby painting a tone of worry over the situation.
Africa’s Rising Debt to China
Over the past two decades, China has significantly intensified its economic engagement with Africa through extensive loans and investments. These initiatives have supported infrastructure projects such as roads, railways, ports, and power plants, helping many countries bridge their infrastructural deficits. However, Africa’s increasing reliance on Chinese capital has led to a staggering debt burden, raising anxieties among economists, policy experts, and local stakeholders.
The Debt Trap Dilemma
The reality of Africa’s debt to China has sparked concerns about the potential risks involved. Critics argue that the terms of these loans are often opaque, disproportionately favoring Chinese companies while burdening African nations with hefty debts and interest rates. This lopsided arrangement can push countries further into debt, creating a vicious cycle that undermines their economic independence in the long run. As the debt burden grows, concerns emerge over the adverse consequences it may have on local businesses, stifling their growth and impeding their ability to compete in the global market.
The Impact on Local Businesses
One of the most significant concerns arising from Africa’s debt to China is the potential erosion of local entrepreneurship and the weakening of domestic industries. As China continues to expand its influence across various sectors, it invariably competes with local businesses, often outmatching them in terms of resources, economies of scale, and competitive pricing.
This puts African firms at a disadvantage, as they struggle to match the aggressive pricing strategies and production capabilities of Chinese enterprises.
Furthermore, China’s dominance in key industries such as manufacturing can lead to the displacement of local businesses, leading to job losses and hindering economic growth. With limited access to financing, technological innovations, and market opportunities, these businesses find it arduous to compete in an uneven playing field. As a result, Africa’s economic landscape risks becoming overly reliant on Chinese imports, undermining the potential growth and development of local enterprises.
Encouraging Economic Self-Reliance
Addressing the concerns surrounding Africa’s debt to China and its impact on local businesses necessitates a multi-faceted approach. African governments and stakeholders must actively work towards strengthening domestic industries by investing in infrastructure and creating an enabling business environment. Prioritizing education, skills development, and fostering
innovation could pave the way for the emergence of robust local businesses that can compete both regionally and globally.
Furthermore, diversifying trade partners and attracting foreign investments from a broader
spectrum of countries could mitigate the overwhelming reliance on China. Encouraging responsible borrowing practices, transparency, and renegotiating unfavorable loan terms could also help alleviate the mounting debt burden and create a more sustainable economic framework.
While Africa’s debt to China has undoubtedly fostered growth and development, concerns over the impact on local businesses continue to trouble policymakers and observers. The erosion of domestic enterprises and the potential long-term economic dependency on Chinese companies are challenges that require urgent attention. It is imperative for Africa to strike a balance between utilizing Chinese investments and preserving economic self-reliance, as the consequences could resonate far beyond business and into the fabric of African societies.
Share
Impact of the US-China Relationship on Africa
Impact of the US-China Relationship on Africa
By Staff Writer

The evolving dynamics between the United States and China have become a central focus in global affairs, influencing numerous regions and economies worldwide. Africa, with its rich resources and growing economic potential, has found itself at the center of this geopolitical tug-of-war. In this assertive analysis, we delve into the impact of the US-China relationship on Africa, recognizing the complex interactions and highlighting key areas of influence.
I. Economic Competition:
1. Infrastructural Development:
Both the US and China have recognized Africa’s immense potential, leading to a race for economic dominance. China, through its Belt and Road Initiative, has significantly invested in infrastructure development, enhancing connectivity across the continent. In contrast, the US has traditionally focused on aid programs and investment in specific sectors, such as healthcare and education.
2. Foreign Direct Investment (FDI):
China’s substantial FDI in Africa has surged, contributing to economic growth, job creation, and technology transfer. However, concerns of dependency and unequal partnerships have arisen due to China’s resource-driven approach. The US, with its emphasis on quality FDI, can offer African nations higher standards, transparency, and sustainability.
II. Geopolitical Influence:
1. Diplomatic Ties and Political Leverage:
China’s presence in Africa has strengthened political relationships, strategically nurturing
alliances to protect its interests. It has been successful in garnering support at international forums and securing access to Africa’s vast natural resources.
Nevertheless, the US possesses deeper historical ties and bipartisan engagement, which it can leverage to strengthen its influence.
2. Countering Security Threats:
In recent years, the US has been actively engaged in countering terrorism and extremism in Africa. Its military support, training, and intelligence cooperation offer African nations assistance in combating security threats. Meanwhile, China has progressively expanded its naval presence in the region, primarily aimed at securing its sea lanes for resource shipments.
III. Socio-cultural Exchanges:
1. Education and Cultural Partnerships:
The US has been a longstanding educational destination for African students, facilitating
human capital development in the region. Cultural ties and exchange programs have further deepened the connection. China, on the other hand, has rapidly increased scholarships and cultural exchanges, fostering people-to-people interactions and understanding.
2. Technological Advancements:
Both the US and China present opportunities for Africa to gain access to advanced technology. While the US offers state-of-the-art technological innovation and knowledge-sharing, China provides affordable digital infrastructure and e-commerce platforms, benefiting African entrepreneurs and modernizing various sectors.
The US-China relationship has left an indelible mark on Africa, fueling an ongoing contest for influence in this resource-rich continent. While China’s economic investments and infrastructure development have significantly impacted the region, the US can leverage its historical ties, quality investments, and focus on democratic values to assert its own influence. Only through a balanced approach can African nations reap the maximum benefits and avoid possible pitfalls of over-reliance or exclusion. The transition towards a symbiotic partnership will demand responsible management and cooperation from both superpowers to support Africa’s sustainable development and self-determination.
Share
Ethiopia Revives an Age-old Question: Access to Sea
Ethiopia Revives an Age-old Question: Access to Sea
By Staff Writer
Ethiopia, a vibrant nation with a population of over 120 million people, has a legitimate right to secure access to the sea. The history books establish that Assab port, situated in present-day Eritrea, historically belonged to Ethiopia. This vital infrastructure, given Ethiopia’s exploding population and its ever growing consumption- cannot continue to be tokenized for political expediency in the region. For centuries, Ethiopia has been an incredibly resilient and self-sustaining nation with a rich and diverse history. However, due to its recent landlocked geographic location, Ethiopia continues to face significant challenges in international trade, connectivity, and overall economic development. Access to the sea is not merely a desire for Ethiopia; it is a critical necessity for the nation’s growth and progress.
Before Eritrea gained independence in 1993, Assab port was an integral part of Ethiopia’s maritime infrastructure, serving as a vital gateway for Ethiopian trade and connecting the nation to the global economy. This historical significance, backed by numerous legitimate historical records, clearly shows Ethiopia’s legitimate claim to the Assab port. The subsequent denial of access to this port after Eritrea’s independence drastically impacted Ethiopia’s economy and hindered its ability to engage in international trade freely.
Furthermore, neglecting Ethiopia’s rightful access to the sea also violates international laws and principles of maritime rights.
The United Nations Convention on the Law of the Sea (UNCLOS) acknowledges landlocked states’ rights to access and utilize the closest seaports and provides legal frameworks to ensure such access. Ethiopia’s plea for its legitimate rights regarding Assab port aligns perfectly with UNCLOS provisions.
The socioeconomic implications of Ethiopia’s landlocked status are profound. Access to the sea would significantly reduce transport costs, boost export opportunities, attract foreign investment, and foster economic growth. This would not only benefit Ethiopia but also have a positive impact on the entire East African region by stimulating regional economic integration and development.
History has shown that when landlocked countries face unjust restrictions on sea access, it often leads to political tensions and the onset of conflict. Ethiopia, being a champion of resilience and persistence in the region, recognizes the importance of regional peace and collaboration. It is undeniable that Ethiopia gaining its rightful access to the sea, the region would witness enhanced stability, cooperation, and shared prosperity.
Ethiopia’s assertive stance regarding its legitimate right to gain access to the sea, particularly through Assab port, is well-founded and resolute. The historical evidence, international legal frameworks, and socioeconomic imperatives all align to solidify this justified claim. Recognizing Ethiopia’s justified calls for sea corridors has implications far beyond meeting domestic demands, but is also a crucial step towards regional peace, stronger economic integration, and a vibrant economic for the entire East African region. It is time for the international community to recognize Ethiopia’s rightful demand and act in accordance with justice and fairness.


